Transaction laundering allows criminals to process illicit payments through legitimate merchant acquirers, posing significant AML compliance challenges. This blog explains the impact of transaction laundering on financial institutions and outlines strategies to mitigate these risks, ensuring robust financial crime compliance.
In the rapidly expanding world of e-commerce, a stealthy and potent threat known as transaction laundering is creating significant challenges for financial institutions. Also called ‘unauthorized aggregation,’ this criminal activity involves an unapproved business secretly processing payments through a legitimate merchant’s account, effectively bypassing the bank’s due diligence.
This process hides illegal transactions within seemingly legitimate payment flows, making it incredibly difficult for authorities to trace illicit funds. In this blog, we will explore the impact of transaction laundering on AML efforts and outline key strategies for effective financial crime compliance.
The Impact of Transaction Laundering on Financial Services
Transaction laundering has severe consequences, exposing merchant services providers (MSPs) and acquiring banks to significant legal, financial, and reputational risks. By unknowingly processing illicit funds, institutions can become unwitting accomplices in criminal activities like money laundering, terrorist financing, and drug trafficking.
The amount of money laundered globally is equivalent to $800 billion–$2 trillion in current US dollars, estimated to be between 2–5% of the global GDP.
If an acquiring bank fails to meet its anti-money laundering (AML) obligations in a transaction laundering case, the damages can be extensive:
- Heavy regulatory penalties and fines
- High chargeback rates and associated fees
- Severe damage to brand reputation
- Complete loss of customer and partner trust
- Potential criminal charges and legal action
Therefore, understanding the intricacies of this threat is the first step toward implementing robust AML measures. Explore how institutions are enhancing AML programs with real-time payment fraud detection to stay ahead.
How Transaction Laundering Works
The process typically involves a series of calculated steps to conceal the origin and nature of illicit funds.
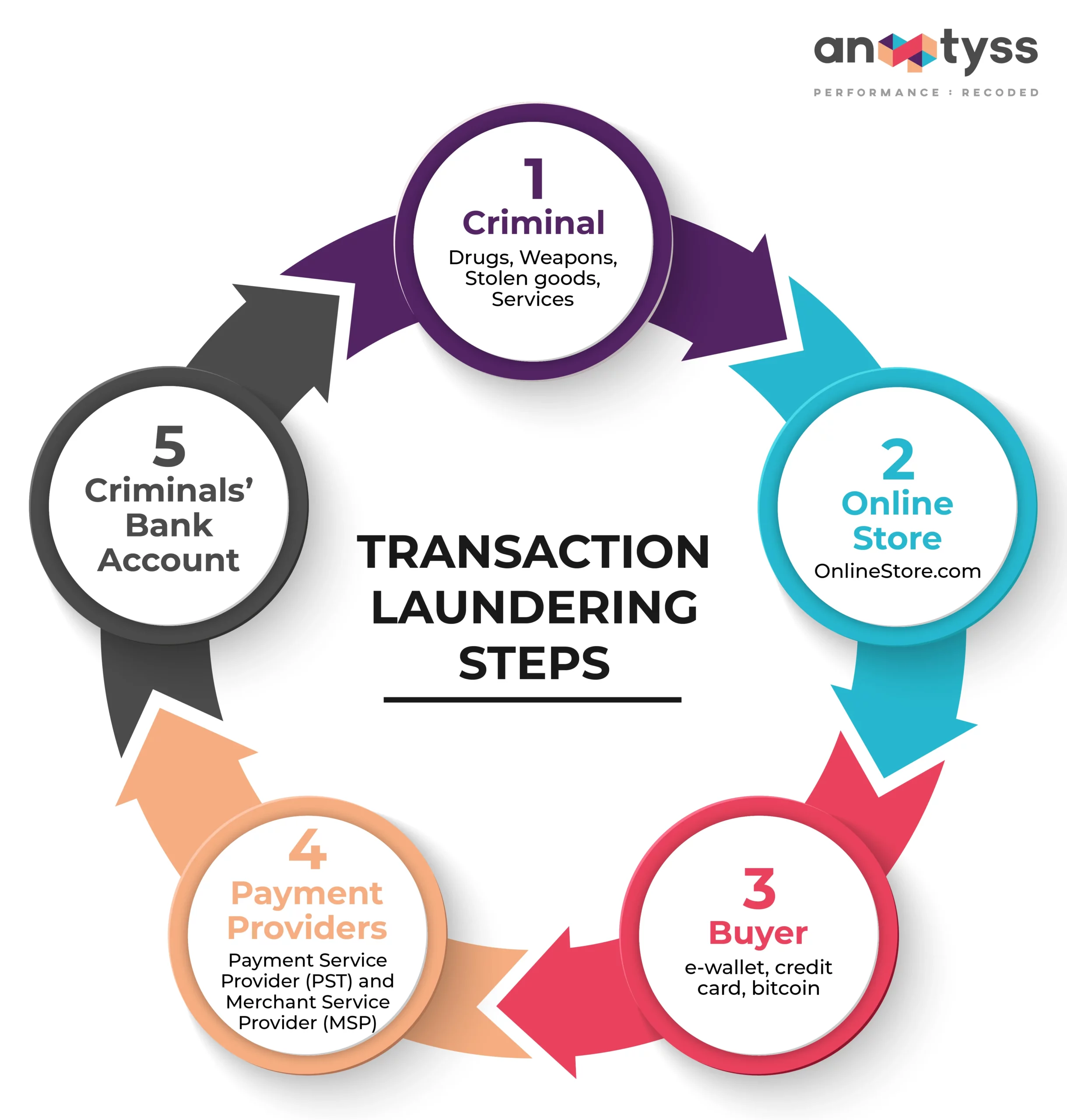
Step 1: Setting Up a Front
Criminals establish a legitimate-seeming online storefront (the “front merchant”) that gets approved by a payment service provider (PSP). In the background, they operate one or more undisclosed websites selling illegal goods or services.
Step 2: Funneling Illicit Sales
When a customer buys something from an illegal site, they are redirected or passed through to the payment page of the legitimate front merchant to complete the transaction.
Step 3: Processing the Payment
The PSP processes the payment, believing it is for a legitimate good or service from the approved front merchant. The funds are then deposited into the criminal’s bank account, successfully laundered.
6 Key Challenges in Identifying Transaction Laundering
Detecting transaction laundering is difficult because it is designed to mimic legitimate activity. Key challenges include:
- Different Risk Profiles
Criminals exploit new payment methods like cryptocurrencies and e-wallets, whose risk profiles differ from traditional methods, making anomalies harder to spot. - Complex Payment Chains
High volumes of small transactions passing through multiple gateways and processors create intricate payment cycles that obscure suspicious patterns. - Website Security Gaps
Legitimate merchants may be unaware their sites are being exploited as pass-throughs for illegal transactions via affiliate programs or as shadow sites. - Advanced Evasion Techniques
Perpetrators use sophisticated methods like anonymization and encryption to hide their tracks, evading traditional detection rules. - Unreported Websites
Criminals can quickly launch professional-looking bogus websites that remain undetected by traditional monitoring long enough to process significant illicit funds. - Cross-Border Complexities
Differing international regulations, currencies, and laws make it challenging to apply a universal detection standard for cross-border regulatory compliance.
Identifying Red Flags for Transaction Laundering
Financial institutions can train their systems and staff to look for the following red flags:
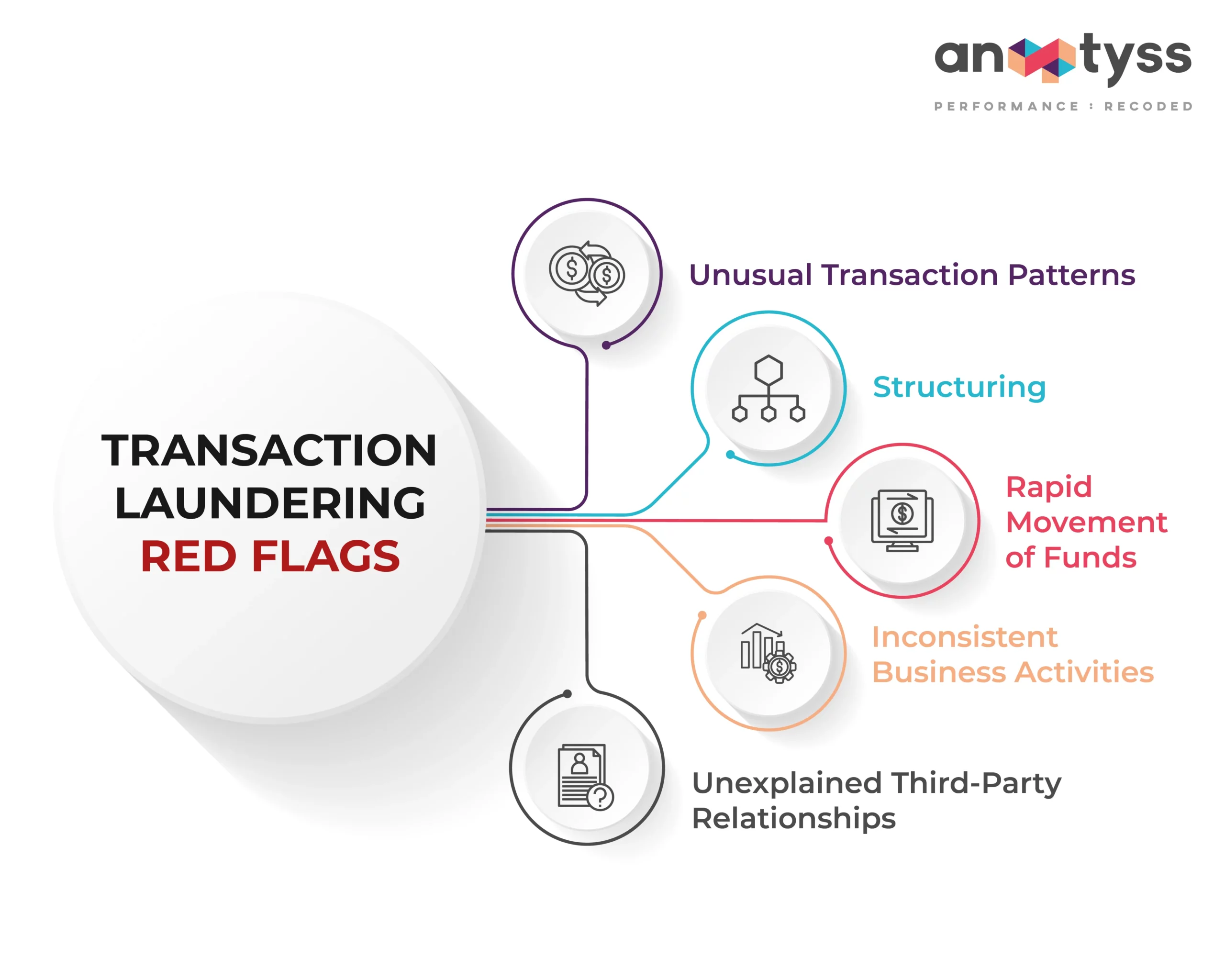
- Unusual Transaction Patterns
A sudden, unexplained spike in transaction volume or a high frequency of small-value transactions inconsistent with the merchant’s history. - High Chargeback Rates
An excessive number of chargebacks with vague reason codes like “product not received” or “product unacceptable” can indicate dissatisfied buyers of illicit goods. - Inconsistent Business Activities
A merchant’s transaction data (e.g., average ticket size, location of buyers) does not align with its stated business model. - Website Mismatches
The business name on the payment descriptor does not match the website that processed the transaction. - Unexplained Third-Party Relationships
Transactions consistently involve unfamiliar or unverified third-party entities without a clear business purpose.
Dive deeper into behavioral red flags with our blog on FATF Red Flags for Money Laundering and Terrorist Financing.
6 Key Strategies to Combat Transaction Laundering
Financial institutions can employ a multi-layered approach to fight against transaction laundering:
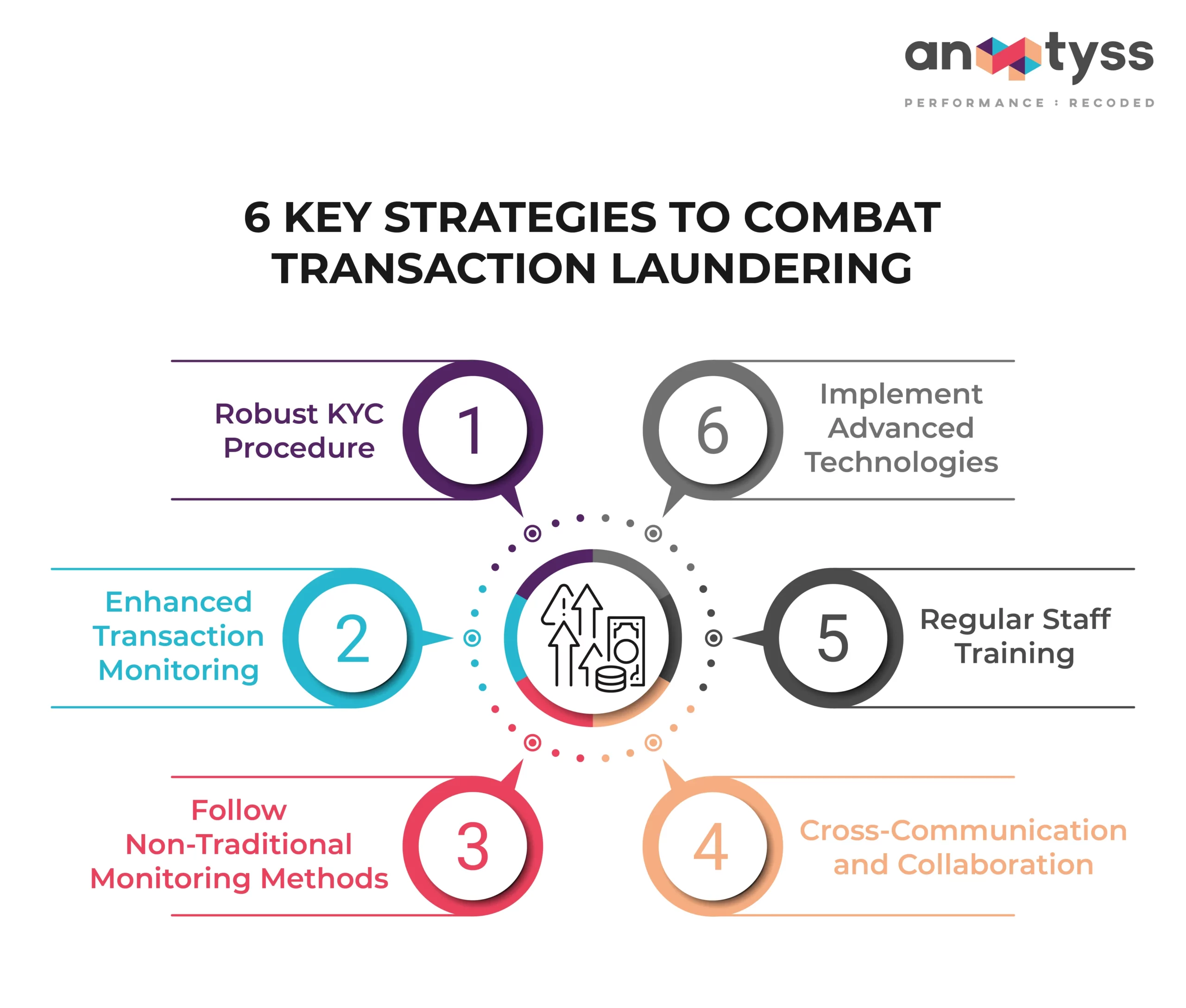
- Robust KYC and Merchant Due Diligence
Implement thorough KYC, Customer Due Diligence (CDD), and Enhanced Due Diligence (EDD) not just for customers, but especially for merchants, to verify their identities and assess the legitimacy of their business activities. For more details, read our guide on what Customer Due Diligence is and how it works. - Enhanced Transaction Monitoring
Utilize a risk-based approach (RBA) to create monitoring rules that specifically look for transaction laundering patterns, such as mismatches between merchant category codes (MCCs) and transaction descriptions. - Website and Social Media Monitoring
Go beyond traditional methods. Proactively monitor the internet for undisclosed websites or social media pages that are funneling payments through approved merchant accounts. - Cross-Industry Collaboration
Establish secure channels to share information with other PSPs, acquiring banks, and law enforcement to identify and report suspicious merchants and websites proactively. - Regular Staff Training
By boosting workforce training, especially for underwriting and risk teams, institutions can strengthen their ability to spot red flags during merchant onboarding and reviews. - Implement Advanced Technologies
Deploy innovative technologies like AI and machine learning to analyze vast datasets and identify complex patterns linked to transaction laundering that rule-based systems might miss. Such tools are transforming how to approach financial crime compliance.
Frequently Asked Questions (FAQ)
- How is transaction laundering different from traditional money laundering?
Traditional money laundering focuses on disguising the source of illicit funds (Placement, Layering, Integration). Transaction laundering is a specific *method* used during the Placement stage, where the criminal uses a legitimate merchant’s payment infrastructure to introduce the money into the system. - What is a merchant acquirer’s responsibility in preventing this?
Merchant acquirers are on the front line. Their responsibilities include conducting thorough due diligence during merchant onboarding, monitoring merchant transaction activity for red flags, investigating suspicious patterns, and terminating relationships with non-compliant merchants. - Can small businesses also be victims of transaction laundering?
Yes. Small businesses with legitimate e-commerce sites can be targeted by criminals who exploit their websites as funnels, often without the business owner’s knowledge. This makes robust website security and monitoring crucial for all online merchants.
Prevent Transaction Laundering and Meet AML Compliance
Transaction laundering is a significant and evolving threat to the integrity of the global financial system. By understanding its mechanics, recognizing the red flags, and implementing robust, multi-layered defensive strategies, financial institutions can protect themselves from severe risks and contribute to a safer financial ecosystem.
See how a US-based bank achieved a 75% reduction in false alerts using our proprietary AML solution—proving that intelligent automation works.
An enterprise-grade solution, such as ALFA, offers a viable path to effectively mitigating financial crime risks, including transaction laundering, and complying with AML regulations. It combines these critical aspects in a customized manner to help financial institutions fulfill their AML obligations.
o learn how ALFA can help your financial institution address financial crime risks and AML compliance challenges, reach out to us at: info@anaptyss.com